- 0 Posts
- 30 Comments

 21·8 months ago
21·8 months agoAnd even that advantage can be minimized by getting any bundle of privacy products, like Proton which offer all of those (Mail, VPN, Drive, Calendar) or even with your self-hosted VPS (Some VPS seller even allow you to prepare it with Nextcloud and a VPN relay for near no extra paiement).
I see the “pay once to one company”, but you also need to trust them entirely, for EVERYTHING.
Also, there’s already plenty of companies doing such thing (regardless of how practical/private/secure they are)
- /e/ with Murena
- Iodé
- Librem (or even morr insane with the Liberty Phone, which is the same thing, made at a maximum in the US…for a different price…)

 1·8 months ago
1·8 months agoJust higher standards.

 1·8 months ago
1·8 months agoThanks for the tip ! To be fair, I haven’t even checked the result and missed on it.

 1·8 months ago
1·8 months agoIt still create an attack vector, as it allows a potential extra method to get access to it, in addition of potential hardware exploits that i shared to gain root. Yes, you can minimize the risks correctly, but the user is the only real barrier against it, not the software anymore. The less potential way to exploit your phone, the better it is. You shouldn’t rely on thinking that such feature is fully attack-proof.

 4·8 months ago
4·8 months agoStop it [send] Mom [send] This is [send] your warning [send] ⚠️ [send] … [send] Did you even read Mom ? [sent 53 photos]
Aggree with common sense, but more difficult to establish with some people.

 1·8 months ago
1·8 months agoThe actual Magisk prompt that ask you if you want to give root to such app. This UI layer.
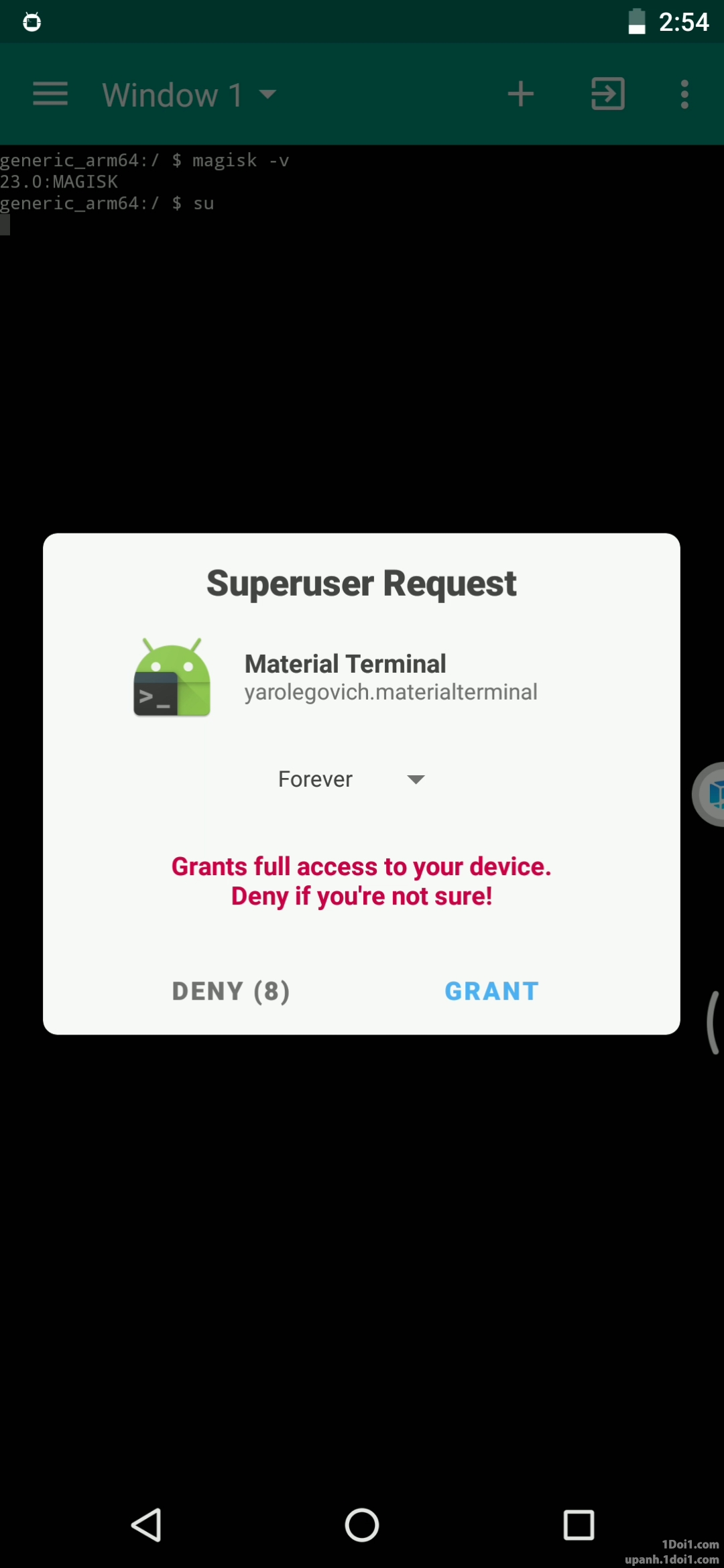
Although, i suppose it could be countered by explicitly refusing all requests or enabling a biometric confirmation


 1·8 months ago
1·8 months agoJust logical. If you gain the privilege to modify system bits, then it just open the potential for attacks abusing root access. And it has been done already. You are just removing one step for them. https://www.bleepingcomputer.com/news/security/loki-trojan-infects-android-libraries-and-system-process-to-get-root-privileges/ https://www.bleepingcomputer.com/news/security/highly-advanced-spydealer-malware-can-root-one-in-four-android-devices/ https://www.bleepingcomputer.com/news/security/new-abstractemu-malware-roots-android-devices-evades-detection/ https://promon.co/security-news/fjordphantom-android-malware/

 1·8 months ago
1·8 months agoOnly big manufacturers can really pay to control entirely the hardware inside it, and allow you to modify it. Checkout Fairphone for example. They’ve been forced to stop hardware security updates due to their chip manufacturer, who refused to continue supporting it, despite them trying to support their devices for plenty more years. This explains the choice with Google.

 1·8 months ago
1·8 months agoSadly, can’t be re-locked. Would have loved to get a Motorola if it was.

 1·8 months ago
1·8 months agoThat’s the main issue really, as it open the possibility to manage your device for anyone getting hold of it. Probably some debug attack methods also with it.

 1·8 months ago
1·8 months agoProove us that you can get better security while remaining able to be fully modified with other phones and brands. https://www.privacyguides.org/en/android/#divestos

 2·8 months ago
2·8 months agoIf you have the UI layer able to grant root access, it has root access itself and is not sandboxed. If the UI layer can grant it, an attacker gaining slight control over it has root access. An accessibility service trivially has root access. A keyboard can probably get root access, and so on. Instead of a tiny little portion of the OS having root access, a massive portion of it does.
In the verified boot threat model, an attacker controls persistent state. If you have persistent root access as a possibility then verified boot doesn’t work since persistent state is entirely trusted.
A userdebug build of AOSP or GrapheneOS has a su binary and an adb root command providing root access via the Android Debug Bridge via physical access using USB. This does still significantly reduce security, particularly since ADB has a network mode that can be enabled. Most of the security model is still intact. This is not what people are referring to when they talk about rooting on Android, they are referring to granting root access to apps via the UI not using it via a shell.

 1710·8 months ago
1710·8 months agoBeat the main purpose of GrapheneOS. Open the phone to a broad lot of security issues.

 7·9 months ago
7·9 months agoDepending if they rely on the G Play Integrity API or SafetyNet Attestation API https://grapheneos.org/articles/attestation-compatibility-guide There’s a secure way to attest it, but if i understand it, it require the app devs to explicitly add support of grapheneOS via hardware attestation API

 1·9 months ago
1·9 months agoIndeed. YACB : Yet Another Call Blocker and SAI : Should I Answer

 3·9 months ago
3·9 months agoFairly certain Silence does allow you to block those. If not, it got plenty of other block options. And it’s Free and Open Source !

 1·9 months ago
1·9 months agoSadly, it hasn’t been updated for more than 2 years, Including the blocklist database. https://gitlab.com/xynngh/YetAnotherCallBlocker_data It seemed to have just used the ShouldIAnswer database, which would have been my suggestion (Even if it isn’t open-source and does more than just block Geo-cals)

 4·9 months ago
4·9 months agoTwo. One classic one and a specific rectangular neck position pillow. I had used only one pillow for years until i met one of my ex. She had around 7 pillows around her bed and used them aplenty, almost as she never wanted to touch the actual bed surface with her head.

It will never make changes as greater as 20% in the most extreme cases. Those tend to be just pre-configured to maximize such gaming performance, often at the cost of security, compatibility and stability. Most of those stuff could be adapted to other distros, and tend to be actually. If a change or piece of software made such important benefit to playing games, without any huge drawbacks, be sure it will surely be soon integrated in other distributions.